21st Apr 2023
Network security is essential to protect your business and data from malicious hackers, malware, unauthorized employees, and other potential threats. Failure to do so could result in financial loss, reputation damage, and legal disputes.
Network security controls encompass both technical and administrative measures to safeguard your company.
Network communication is now an integral component of business operations. Not only does it allow companies to communicate among themselves but also with clients and customers. Unfortunately, much of this communication may contain sensitive information that must be protected.
A reliable locking system is one of the essential security tools an organization can have to keep its communications private and prevent unauthorized access. Which type of lock you select will depend on your business needs and what you wish to protect.
For instance, you might opt for a lock that has an ANSI grade rating. This standard was established by the American National Standards Institute to guarantee strong security protocols in locks.
The ANSI rating is determined by several criteria, such as how well a lock can resist manipulation by hackers. Furthermore, some locks can be programmed with duress mode–a silent alarm that notifies the owner if an unauthorized individual attempts to open the door.
Network security methods must evolve and adapt in response to new threats, making it the responsibility of everyone on the team. When developing your overall security strategy, ensure you consider each layer of the network for protection.
Network security measures typically involve authentication, network access control (NAC), and encryption. For instance, a NAC system might use MAC address control to identify all devices connecting to the network and restrict their access to certain components of it.
Authentication is the process of verifying an individual or machine is who they say they are, and it is an essential element in network communication security. It guarantees only those with authorized credentials can access sensitive systems, protecting organizations against unauthorized data breaches.
Network-level authentication is the practice of distinguishing legitimate users from malicious ones by cross-checking usernames against a list of approved ones. This type of verification is commonly employed in Wi-Fi, email, and web browsing networks alike.
When it comes to authentication methods, there are various options. Passwords, security tokens, biometric verification, and phone/text confirmations can all be utilized depending on your organization’s needs; you just need to ensure they’re consistent across all systems.
In today’s cybercriminal-driven world, reliable authentication and authorization are essential requirements. Data breaches have seen a meteoric rise over the years, making it harder for businesses to stay ahead of hackers.
Combining the strength of an authentication system with other security measures, you can guarantee your network is safeguarded from a variety of threats. This makes it a suitable solution for both small and large enterprises alike.
Authentication can be a complex process, so if you’re unfamiliar with it, here’s some background:
Multiple layers of verification are necessary to confirm a user is who they say they are. This could include traditional username and password authentication, security tokens, biometric data like fingerprint scans, as well as other factors like location and time.
Reliability is the ability of a system or component to perform as expected under specified conditions for an extended period. Reliable products can range from cars that start automatically when you turn the key, aircraft that fly safely through turbulent airspace, medical devices that work correctly when applied on patients, and telephone switchboards which connect calls correctly.
Reliability can be assessed in a number of ways, depending on the research you conduct and the method chosen. Common methods include test-retest reliability, parallel forms reliability, and internal consistency reliability.
Test-retest reliability refers to the correlation between scores given on a similar test to different groups at various times. It’s especially critical for tests with long-term stability, like intelligence tests. Reliability can be assessed through graphing data and computing a measure called Pearson’s r.
Another type of reliability is inter-rater reliability, which measures the correlation between a group’s judgments on an exam. This type of consistency is especially critical in behavioral science research when groups that are unfamiliar with each other must collaborate.
Reliability should be part of your product design and development process, so it’s best to have a team responsible for it throughout each stage of production. This includes the design/engineering team, manufacturing team, and procurement group. These departments should be well-integrated, so that product reliability remains top of mind in all areas of your business.
Network communication security is a multi-layered endeavor encompassing authentication, access control, and encryption. Ensuring all systems are protected is vital as it can protect your organization from financial losses or regulatory fines.
You can safeguard your system by creating a clear network topology. Doing this helps eliminate security flaws and stops attackers from accessing sensitive company information. Furthermore, it prevents employees from connecting to an unauthorized network, thus denying them unauthorized access to your data.
Furthermore, you need a reliable locking system to safeguard your data. This includes installing a firewall between your company’s internal network and external networks. Firewalls regulate incoming and outgoing traffic by specifying the protocols used.
A firewall also shields you against malware, viruses, and other potential threats. These types of incidents can do extensive harm to both your company’s reputation and financial well-being.
Another way to increase system reliability is by de-rating components that are under heavy load. This reduces the overall stress on a component, thus increasing its lifespan.
With the right combination of technologies, you can connect your building with intelligent sensors and programmable controllers. These products are capable of communicating with each other through reliable industry-standard protocols and scalable software.
A reliable locking system offers many benefits for various business applications. In retail environments, employees often need to use multiple keys in order to open cabinets and display merchandise to customers; this wastes time and causes customer frustration. Likewise, hospitals or healthcare settings where unsecured medications or documents pose risks to both patients and staff must consider using a reliable locking system as well.
Electronic locks offer the advantage of restricting access to specific areas and eliminating individual keys, saving money on locksmith visits and maintenance. Plus, it makes tracking employee movement around your facility much simpler.
Some electronic locks also come with features designed to make them more secure, such as duress mode. With this setting, the lock will send a silent alert to the security room if an unauthorized individual enters a code that is one digit higher or lower than its valid user code. Furthermore, some models will block access if four invalid combinations have been entered consecutively.
Wireless locking systems have become increasingly popular in both commercial and residential applications since they don’t need AC power and can be placed nearly anywhere within a building. However, some limitations exist; for instance, 2.4GHz Wi-Fi is often employed but generates excessive communication traffic in densely populated buildings, making it less reliable than 900MHz solutions.

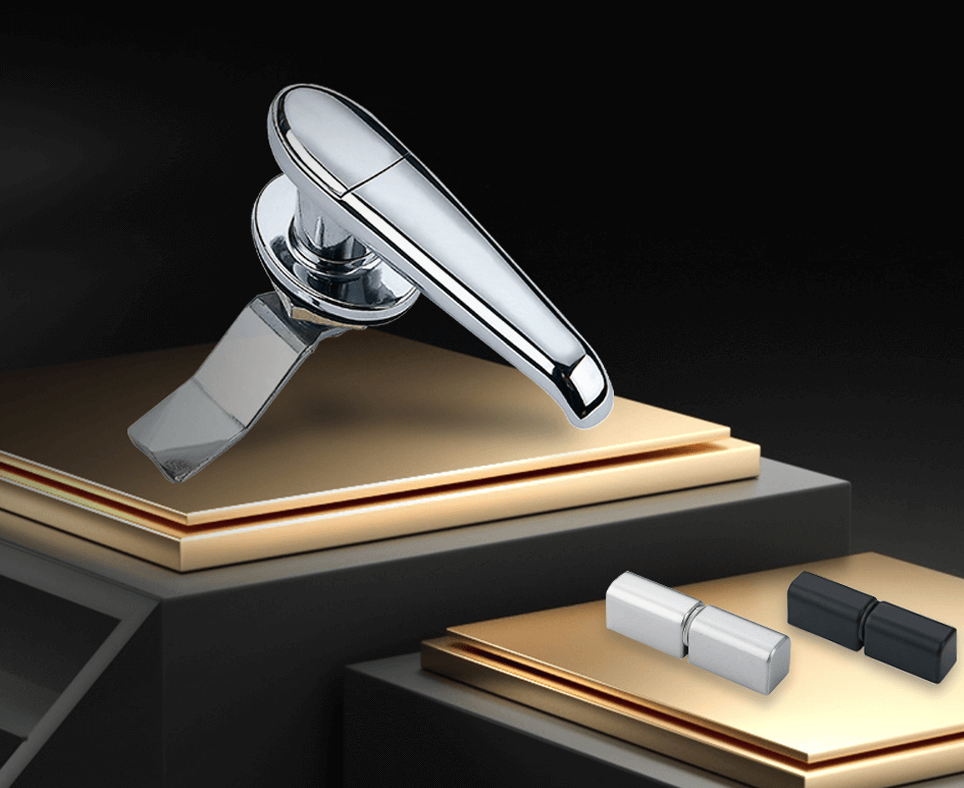

ZONZEN Automated Lock Manufacturers is an OEM Industrial Locks Company that has earned many satisfied OEM projects for rod lock wholesalers and brand owners with glowing testimonials. Their products can be found in the communications, power, and mechanical equipment industries.
Our Customer service is unsurpassed. We have well trained customer service representatives that are ready to help you with your next project be it large or small.
Our R&D team keeps developing new items for customers all over the world to ensure that we keep the flow of new hot selling point. If you have any questions or suggestions, please do not hesitate to contact us for further assistance.